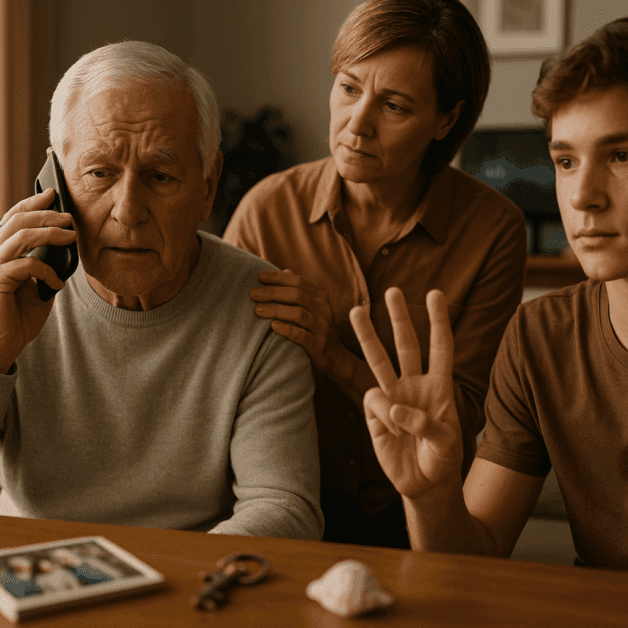
Grandparent Scams Using AI Voice – The 3 Verification Questions Every Family Should Agree On
Families should agree on 3 verification questions (a private safe-word, a known-only detail, and a callback-to-a-known-number rule) to stop AI voice grandparent scams. AI can clone a familiar voice from only a few seconds of audio, so voice alone isn’t proof. This article explains the questions, how to use them, and what to do if […]